By William Callahan
Computer Security awareness is imperative to any end user; WiFi security is no exception. John Adams, the speaker for the DACS General Meeting in January, presented an excellent set of information which was invaluable to understanding wireless devices and securing them from malicious attacks.
John kicked off the meeting by exploring the concepts of the 2.4GHz and 5GHz WiFi bands. Currently, most modern devices are “dual-band”, meaning that they support both the legacy 2.4GHz band and the modern 5GHz band. Most wireless routers which are “dual band” provide backwards compatibility to support devices that are not compatible with the 5GHz band. However, although the 5GHz is the latest WiFi band, John explained how the new band may not be better. For example, the 2.4GHz band is able to provide a signal which has a greater range and greater ability to penetrate solid objects than the 5GHz band. However, the 5GHz band will provide a significantly greater speed if you can accept a shorter operating distance. Additionally, the 5GHz band provides up to 23 consumer channels compared to the 11 available on the 2.4GHz band. The expanded number of channels on the 5GHz band is a significant improvement for areas where WiFi congestion is common, allowing devices to have a higher probability of using a dedicated channel. In the end, the user must make the ultimate decision of which band to use, based on their environment and device requirements.

WiFi performance can be directly affected by a number of variables related to which WiFi channel is used. Interference from other devices, for example, can greatly reduce the performance of your WiFi. Additionally, cross-talk between channels (when radio frequencies overlap) can cause serious performance hits. This brings up a fairly controversial question: which channel is the best? Several people argue that channels 1, 6, and 11 of the 2.4GHz band are the best channels, given that they are well spread apart, causing little to no crosstalk. However, John felt that this may not always be the case. Going back to issues with interference, it is next to impossible to guarantee that any one channel will always be the best. At any given point in time, a device can unexpectedly interfere with a channel which you have statically chosen. Therefore, the router should be set to automatically determine the best channel.
While the channel which is chosen may have no effect on WiFi performance, the number of devices connected will do so. This is due to the fact that devices that utilize the same access point will share the same channel. Therefore, if all other channels are not being used by another device, the channel used by the wireless router will have no effect on performance. In this case, the number of devices connected at any given point in time will affect the performance of the WiFi network. This is because each device must wait for its turn to communicate with the router, effectively sharing the same channel.
John brought to our attention a major security flaw in the WiFi Protected Setup (WPS) standard. The WPS standard allows end users to easily and seamlessly connect their wireless devices to an access point or wireless router. Generally, the user invokes the WPS service by requesting it on their device and pressing the WPS button on their wireless router. In addition to pressing the setup button, many routers have the capability to require a Personal Identification Number (PIN) as part of the WPS service. Of course this seems like a good idea. However, John made the important point that introduction of this PIN completely undermines the security authentication of even WiFi Protected Access II (WPA2) security provided by a wireless router. An attacker can easily utilize a brute force attack method to guess the PIN of the WPS service and gain access to the network. In particular, the PIN is flawed in that only the first four digits must be guessed while the last four are calculated, significantly reducing the possible number of PIN numbers. Not to mention that many routers do not timeout if an incorrect PIN is provided, allowing the PIN to be guessed quickly. John recommended that this vulnerability can be eliminated by disabling the PIN option of a router which supports WPS.
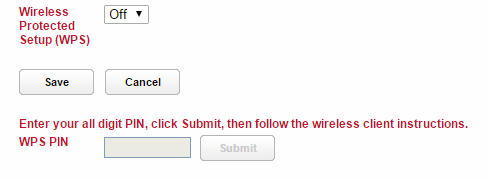
WPS Pin Setting in AT&T/Frontier Wireless Router Network Settings
Finally, users should be aware of the security implications of utilizing public networks. Commonly, people take advantage of free WiFi available at places like coffee shops. Therein lies an issue; any unprotected network which end users connect to provides attackers with a unique opportunity to steal data. The user should be aware of their environment and choose the appropriate firewall settings. Microsoft Windows, for example, will ask the user to provide what type of network they are connected to: Home, Work, or Public, Public being the most secure of all the settings. In addition, users should be self-aware of what data they access through the network they are connected to. For example, if a website contains sensitive information, the user should only utilize that service over a secure connection such as Hyper-Text Transfer Protocol Secure (HTTPS) with a trusted Secure Sockets Layer (SSL) Certificate. Otherwise, hackers could use packet sniffing tools or even eavesdrop on the WiFi channel you are using to take data being transmitted.
In my personal opinion, John’s presentation was clear but also comprehensive. I am surprised that I learned so much about a topic in which I felt I was already knowledgeable. John was able to keep the audience engaged by providing opportunities for discussion across each topic he explained in detail. The one concept to take home from John’s presentation was to realize that anyone and everyone is a target of malicious hackers. While you may believe that you have nothing to hide, this is the exact frame of mind which hackers tend to target; protect your data to protect yourself.
