DACS guru Bruce Preston was our presenter at the November 2014 general meeting on the topic of secure digital communications. He covered a lot of technical content but made it accessible by relating it to historical and current use of the technology for encrypting data.
First he got some definitions out of the way. A code is a way to represent information. For example the Roman alphabet is a way to represent the words of a spoken language like English. Morse code is a way to represent words with a series of dots and dashes and spaces transmitted electrically over a telegraph wire. Herman Hollerith invented a way to represent characters with punch combinations in columns of a card with 80 columns and 12 punch positions each. ASCII is a computer code that represents each character using 7 binary digits.
A cipher is a way to keep information secret from those who are not the intended recipients. The process is called encryption. Symmetric key ciphers use the same key to encrypt and decrypt the data. A simple example of a cipher is to shift the alphabet by several letters, so A might map to F, B would map to G, and so on. A more complicated cipher uses a pre-shared key (PSK) that shifts each letter by a differing amount determined by the PSK, a maximum length of 26 characters, which is repeated until the end of the message.
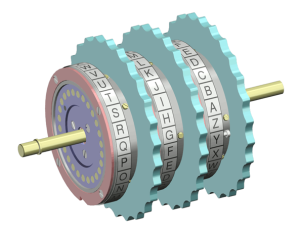
The Germans used a much more complicated cipher during World War II involving their Enigma machine which had three rotors. Each character was shifted 26 times for each of the three rotors. Therefore the substitution key was not repeated for 26 cubed (17,256) characters. This would effectively have been an unbreakable cipher, but the Polish intelligence service managed to capture an Enigma machine and sent it to the British before Poland was invaded. Later in the war a German submarine was captured along with a top-secret book of rotor settings, which was the other information needed to break the code, although the British analysts, headed by mathematician Alan Turing, had already made progress before then.
Another example of a symmetric cipher is used in Wi-Fi. The pass phrase used by all the devices on the network is the pre-shared key.
Asymmetric key ciphers use one key to encrypt and a different key to decrypt a message. An example is Public Key Encryption (PKE) which uses a combination of the sender’s private key and the recipient’s public key, or vice versa. This can be used to establish a Secure Sockets Layer (SSL) connection with a web server, such as your bank’s. The public key is stored in the server’s digital certificate, whose authenticity is verified by the use of an encrypted certificate of another party who vouches for them. Eventually a certificate authority (CA) is reached, such as VeriSign, Thawte, Geosign, etc., whose authenticity is verified based on a list of CAs whose public keys were previously stored on your computer.
A final example of an asymmetric cipher is a virtual private network (VPN) used to connect two separated local area networks (LANs), or a portable machine and a company LAN. There is a VPN router at each end of the connection, or a client program on the portable computer in that case.
Bruce’s presentation was a great mini course on the subject, and he has made his slides available for posting on the DACS Downloads page. The story of the Enigma machine was especially interesting, and I plan to do more reading on Alan Turing. There’s even an upcoming movie, The Imitation Game, on the subject of the British cracking the Enigma code.